Take measures to protect your computer data from ramsomware.
Subscribe now for unlimited access.
$0/
(min cost $0)
or signup to continue reading
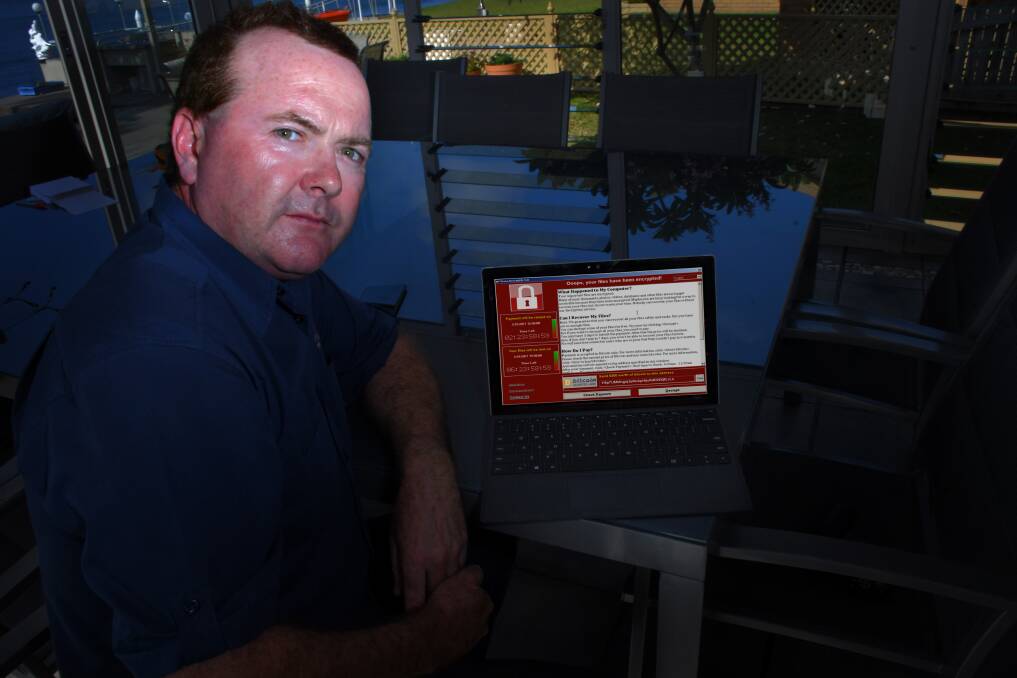
That’s the warning to Mid-North Coast business owners from Port Macquarie IT expert Steve Laws after four of his clients had their computer data held “hostage” by digital extortionists recently.
Typically embedded within a harmless looking email, ransomware is malicious software that disables a computer’s antivirus software and backup systems before effectively holding its data “hostage” with an unbreakable 512-bit digital encryption key.
With the data securely locked, the attacker demands a “ransom” in return for the key that will release it.
The ransom is usually paid in bitcoin because the digital currency’s trail is extremely difficult to follow.
Mr Laws, owner of Home and Office Computer Solutions, said ransomware attack cost a Mid-North Coast accountancy firm $25,000 to have their files unlocked.
A local medical specialist paid a “ransom” of $1800 to retrieve patient files, an auto parts store owner more than $3000 and a share trader $800.
‘Like a death in family’
Although the accountancy firm was not a client, Mr Laws was called in by the principal to assess the damage the ransomware attack had wrought.
“It’s the first time in my 20-year career in IT that I had to tell someone that there was absolutely nothing I could do,” Mr Laws said.
“It was very traumatic: I felt like I was telling him that there had been a death in his family.
“His accountancy business had effectively disappeared.
“His client’s files, ATO applications, business accounts, the work templates he’d built up over years… everything was locked up and there was no way to unlock it without paying the ransom.”
Initially working day and night, it took Mr Laws six days to assess the scope of the attack on the firm, help to arrange payment and secure the encryption key that unlocked the data.
Backing up data to one or more external USB drives will not stop ransomware, Mr Laws said.
The only way to guarantee data is protected is to use a NAS (Network Attached Storage) system, a small file server that uses encrypted usernames and passwords to protect data.
The removable NAS can only be accessed using the company’s unique encrypted username and password, which is not stored on any Windows machine.
Arrange for a security audit
Mr Laws believes his four clients are just the tip of a ransomware “iceberg”: It’s likely there are numerous other local victims.
Australian businesses, government agencies, academic institutions, and even law enforcement agencies have been victims of ransomware attacks in recent years, as well as home computer systems.
Mr Laws said all computer users – not just business owners – should have strong passwords on all network accounts and be vigilant checking emails they receive.
He advises scrutinising new email while it’s still in your inbox, checking the sender’s address before opening it or clicking on web links within it.
He urged business owners to have a reputable IT specialist conduct a thorough security audit to determine if they need to take additional precautions and how best to protect their network and data.
“The people who make malicious software and Trojans are well aware of what security measures IT professionals can take,” he said.
“They adapt their virus to counter the safeguards we put in place.
“The IT industry is constantly trying to come up with ways to stay ahead – not always successfully.”
Malware ‘increasingly sophisticated’
Most ransomware viruses come in the form of a URL link embedded within an email that appears at first glance to be from a legitimate source, such as a well-known phone company or power supplier.
“People open these emails without thinking too much about it,” Mr Laws said.
“When you click on links within them, you are basically like saying ‘Yes, I want to proceed and install this software’.
“Windows and the various anti-virus products will generally allow you to do so if you choose to do so. Once you open the link, the virus begins downloading in the background, out of sight.”
Ransomware first emerged in Russia in 2005.
Newer versions have become increasingly sophisticated, able to disable the computer’s antivirus and hard drive backup systems before slowly – sometimes over weeks – encrypting files.
Ransomware can affect Windows-based or Apple iOS machines, as well as mobile phones and tablets.
The software can also encrypt files in Cloud-based services such Google Drive, One Drive and DropBox.
However, once the ransom is paid, there is no guarantee the key will be sent: Many companies have been left out of pocket and with no way to access their files.
Affordable solution foils ransomware
The cost of the NAS, installing the software that runs it and the dual 4-terabyte (TB) hard drives that make up the solution is around $1650 for a single desktop and $150 for each additional computer.
For companies running a server, the NAS solution costs around $2800, depending on the hardware required.
Depending on configuration requirements, the NAS runs two 2TB or two 4TB drives that are specifically designed to run around the clock in a NAS environment.
Hardware or backup failures, intrusion attempts, and maintenance notifications are sent via email to the network manager.
The NAS also has three USB 3.0 ports.
Whenever an external drive is connected to a port, all backup data is automatically copied to the external drive from the NAS.
Once the copy/transfer is complete, the user receives a notification email telling them the drive can be removed from the network – ideally to a separate location.
This procedure guarantees safe data backup, proactive notification, and offsite and onsite protection.

